Researchers Discover Critical GitHub CVE-2026-3854 RCE Flaw Exploitable via Single Git Push
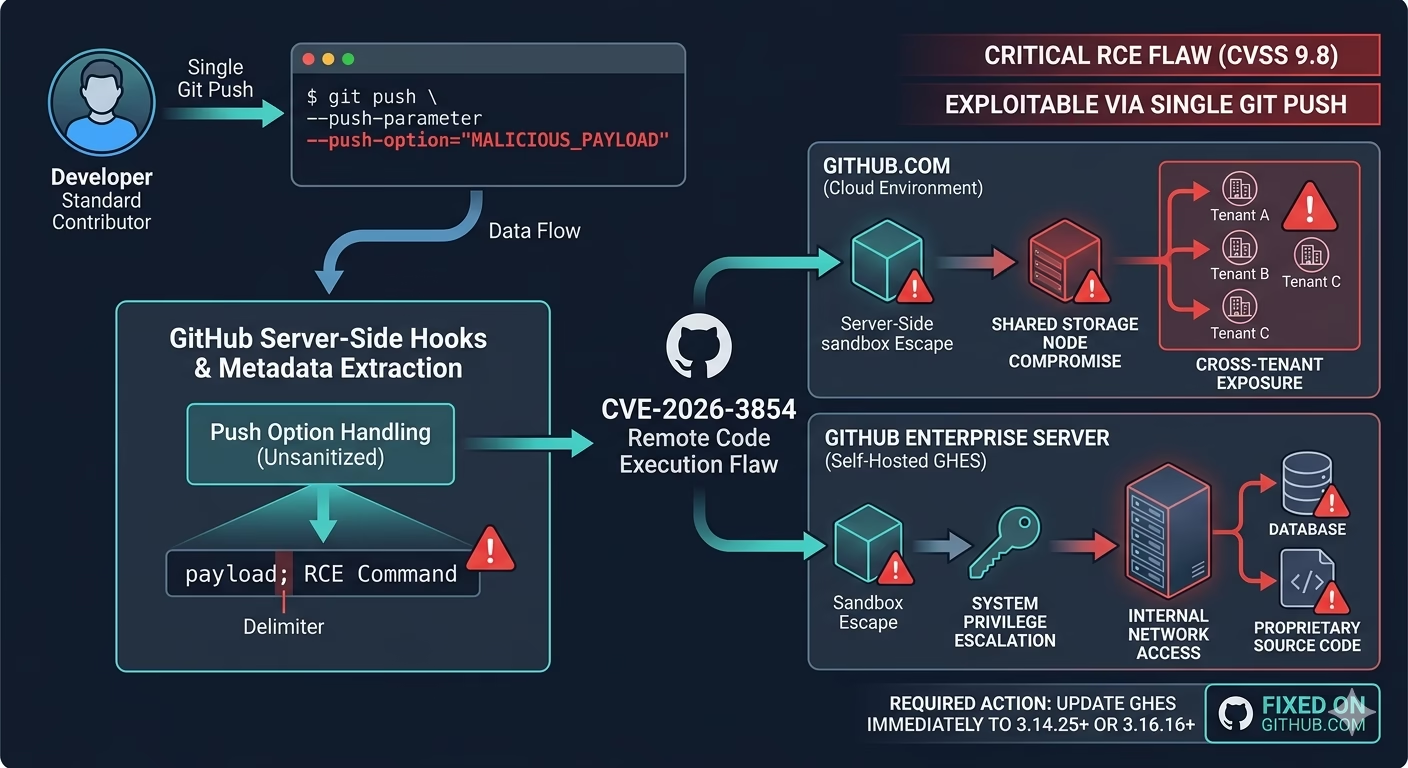
The global developer community has been placed on high alert following the disclosure of a severe security vulnerability within the world’s most popular version control platform. Researchers discover critical GitHub CVE-2026-3854 RCE flaw, a vulnerability that strikes at the heart of how GitHub handles internal communications. With a CVSS score indicating extreme severity, this flaw allows for Remote Code Execution (RCE), giving attackers a potential doorway into the core infrastructure of both cloud and enterprise environments.
The most chilling aspect of this discovery is the attack vector: researchers discover critical GitHub CVE-2026-3854 RCE flaw exploitable via single git push. This means that any user with standard push access to a repository could, in theory, compromise the entire server with one simple command.
1. The Core of the Vulnerability: Unsanitized Push Options
At its technical root, CVE-2026-3854 is an “Improper Neutralization of Special Elements” vulnerability. GitHub allows developers to pass additional metadata to the server using the --push-option flag during a standard git push. Security researchers from Wiz found that these user-supplied values were not properly sanitized before being embedded into internal service headers. Because the internal header format used a specific delimiter character that could also be included in user input, it opened the door for “Command Injection.”
2. Exploiting Internal Protocol Trust
Modern cloud architectures like GitHub’s rely on multiple microservices communicating with each other. This flaw exploits the “implicit trust” between these services. When a developer pushes code, one service generates a metadata header (the X-Stat header) and passes it to a downstream service. By injecting a semicolon or other delimiter into the push option, an attacker can “trick” the second service into reading a new, malicious command as if it were a legitimate instruction from the first service.
3. The “Push-to-Own” Attack Chain
The exploitation of CVE-2026-3854 is remarkably straightforward for a flaw of this magnitude. A researcher or attacker only needs a standard Git client and legitimate push access to any repository on the target instance. By chaining three specific injections—manipulating the rails_env value, redirecting the custom_hooks_dir, and triggering path traversal—they can bypass all standard security sandboxes. This results in the server executing code with the same privileges as the “git” service user.
4. Risks to GitHub Enterprise Server (GHES)
While GitHub.com was patched rapidly, the risk remains significant for organizations running GitHub Enterprise Server (GHES). On a self-hosted GHES instance, a successful exploit leads to a full system compromise. An attacker could gain read/write access to the entire filesystem, view sensitive internal service configurations, and potentially access every single repository hosted on the server, even those they shouldn’t have access to.
5. Multi-Tenancy and Cross-Tenant Exposure
On the public GitHub.com cloud, the vulnerability posed a different but equally terrifying threat: cross-tenant exposure. Due to GitHub’s shared backend infrastructure, obtaining RCE on a shared storage node could allow an attacker to read millions of repositories belonging to other users and organizations. This effectively breaks the “isolation” that cloud users rely on to keep their private code secure.
6. The Role of AI in Vulnerability Discovery
In a fascinating twist, Wiz researchers noted that this was one of the first major critical vulnerabilities discovered in closed-source binaries using AI. By using advanced AI models to analyze the binary logic of GitHub’s internal services, researchers were able to identify the injection point that had previously escaped manual audits. This signals a major shift in the cybersecurity landscape, where AI is now a primary tool for both finding and fixing “zero-day” exploits.
7. Immediate Mitigation and Patching Timeline
GitHub has been exemplary in its response. Within two hours of the initial report on March 4, 2026, the vulnerability was mitigated on GitHub.com. For Enterprise customers, GitHub released a series of critical security updates. Administrators are urged to update to the latest versions of GHES immediately. At the time of public disclosure in late April 2026, data suggested that nearly 88% of self-hosted instances were still running vulnerable versions, leaving a massive window for potential exploitation.
8. Lessons for the DevSecOps Community
The case of CVE-2026-3854 serves as a wake-up call for the broader software supply chain. It highlights that even “trusted” internal protocols must treat all user-controlled data as potentially malicious. Security experts recommend that organizations not only patch their servers but also implement “Least Privilege” access controls and monitor their Git server logs for suspicious push-option patterns involving unusual characters or long strings.
Frequently Asked Questions (FAQs)
1. What makes CVE-2026-3854 a “Critical” flaw?
It is critical because it allows Remote Code Execution (RCE). An attacker doesn’t just steal data; they take control of the server processing the code, which can lead to a total infrastructure breach.
2. Can someone hack my GitHub account using this?
Not exactly. This is a “server-side” flaw. It allows an attacker to compromise GitHub’s servers, not your individual password. However, if the server is compromised, your private code could be stolen.
3. I use GitHub.com; do I need to do anything?
No action is required for GitHub.com (Cloud) users, as the security team patched the cloud environment within hours of discovery. No evidence of unauthorized data access was found.
4. Which versions of GitHub Enterprise Server are affected?
All versions of GHES prior to the April 2026 security patches are affected. Specifically, you should upgrade to versions 3.14.25, 3.15.20, 3.16.16, or later, depending on your current release track.
5. Is a single git push really enough to trigger the hack?
Yes. Because the vulnerability is triggered during the server’s automatic processing of the metadata sent during a push, a single command like git push --push-option="malicious_code" is enough to initiate the attack chain.
🚀 Build a Powerful Online Presence with RojrzTech
Quiet updates often carry the loudest consequencesIn an ever-evolving digital landscape, brands grow by adapting fast and executing smart. RojrzTech offers customized solutions in web development, UI/UX design, SEO, branding, and social media—helping businesses improve visibility, engagement, and overall digital performance.
📩 Start Growing Your Digital Presence Today
Partner with RojrzTech to craft digital experiences designed for long-term success and real audience connection. Let’s build an online presence that works harder for your business